Hackviser+scenarios
This cross-cloud scenario is unique to the platform. You start with a set of stolen OAuth tokens (simulated via Hackviser’s identity vault). You have no direct network access to the corporate LAN.
Hackviser presents a custom web app with a Time-Based Blind SQL Injection vulnerability. But here is the scenario constraint: the network has a jitter of 300ms. Simple delays (WAITFOR DELAY) are unreliable. hackviser+scenarios
To truly understand its power, one must move beyond feature lists and dive into . These are not mere walkthroughs; they are dynamic, multi-layered attack simulations that mirror the chaos of a real red team engagement. This cross-cloud scenario is unique to the platform
This is a time-based scenario. The Hackviser dashboard shows a "Stealth Meter" that depletes if you generate suspicious Event Logs. Hackviser presents a custom web app with a
Hackviser integrates virtualized ICS (Industrial Control Systems) components. You are presented with a Modbus TCP simulation.
From bypassing EDR with Living-off-the-Land techniques to pivoting from Azure to an air-gapped PLC, these scenarios force you to abandon the "happy path" of hacking. They force you to struggle, to network pivot, and to write your own tools.

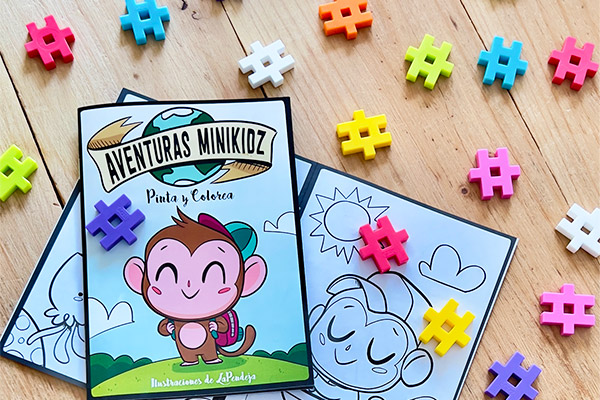 Te regalamos con tu pedido nuestro librito para colorear Aventuras Minikidz más un pack de piezas Meli para jugar y disfrutar.
Te regalamos con tu pedido nuestro librito para colorear Aventuras Minikidz más un pack de piezas Meli para jugar y disfrutar.