Software Classes Clsid 86ca1aa034aa4e8ba50950c905bae2a2 Inprocserver32 F Ve — Reg Add Hkcu
Learn more!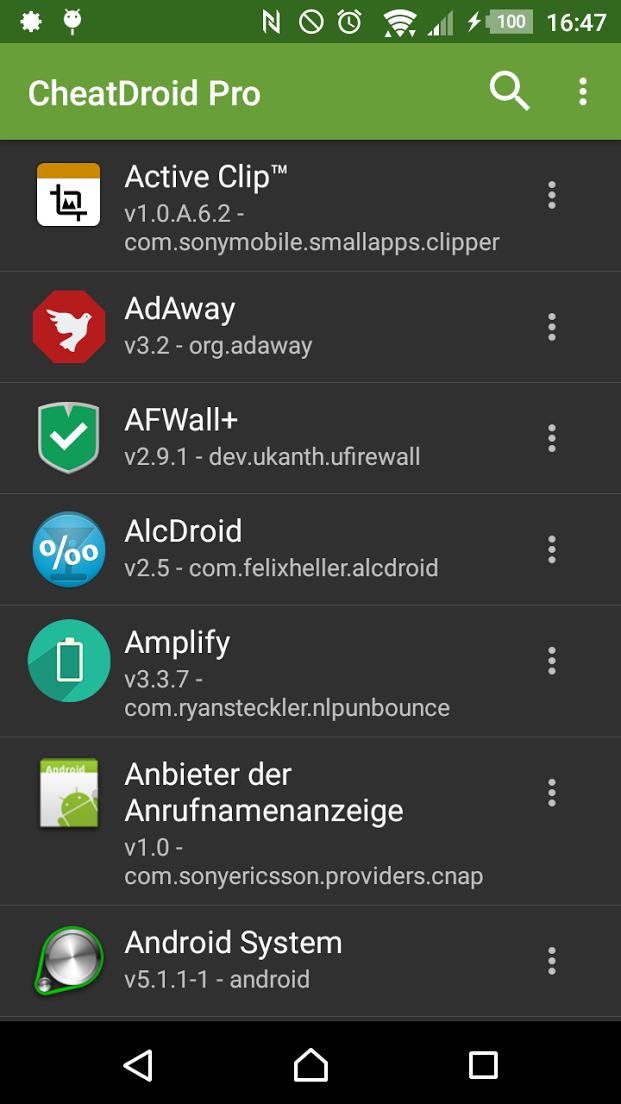
Download Cheat Droid only from here in order to prevent yourself from fakes and viruses.
Unfortunately, it is not possible to perform Android Cheats without a rooted device.
Perfect for debugging self-developed apps or finding security vulnerabilities!
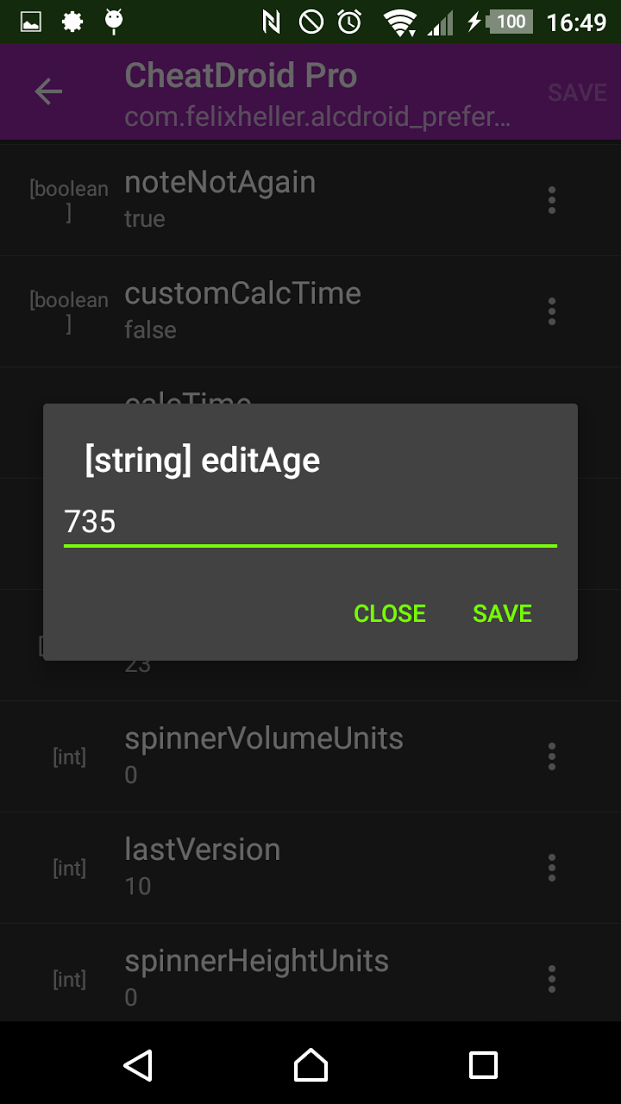
Comes with a Shared Preferences editor, a Text Editor and a SQLite Browser!
Revert and Restore Android Cheats!
reg add HKCU\Software\Classes\CLSID\random-GUID\InprocServer32 /ve /d "C:\Users\Public\malware.dll" /f Then triggers a legitimate application that normally loads the intended DLL. Because HKCU has priority, the malicious DLL loads instead. Attackers don’t need to add a Run key. They wait for any application to instantiate a specific CLSID — sometimes one used by Explorer, Office, or browsers. Every time that COM object is called, the malware runs. Method 3: Bypassing Security Software Registry-only persistence (no new file in startup folder) often evades simple antivirus scans. By the time you see the reg add command in logs, the malware may already be active. Part 5: Analyzing Your System for This Registry Key Step 1 – Check if the key exists Open Command Prompt as Administrator and run:
It is important to clarify upfront: the string of characters you’ve provided — 86ca1aa034aa4e8ba50950c905bae2a2 — does not correspond to a standard, documented Windows CLSID. Known CLSIDs are typically well-documented (e.g., 00024500-0000-0000-C000-000000000046 for Microsoft Office or 0002DF01-0000-0000-C000-000000000046 for Internet Explorer). The sequence you’ve listed appears either randomly generated, truncated, corrupt, or potentially associated with that uses random GUIDs to hide registry entries. They wait for any application to instantiate a